Trusted by Security Teams Worldwide
Our platform delivers measurable results for organizations of all sizes
99.9%
Uptime
Reliability
85%
Reduction in
Response Time
10B+
Events Processed
Daily
500+
Enterprise
Customers
Respond to incidents faster and smarter with automated
workflows, advanced log analysis, and centralized monitoring.
Our SOAR Automation platform helps security teams automate response workflows, analyze logs efficiently, and monitor their infrastructure from a single pane of glass.
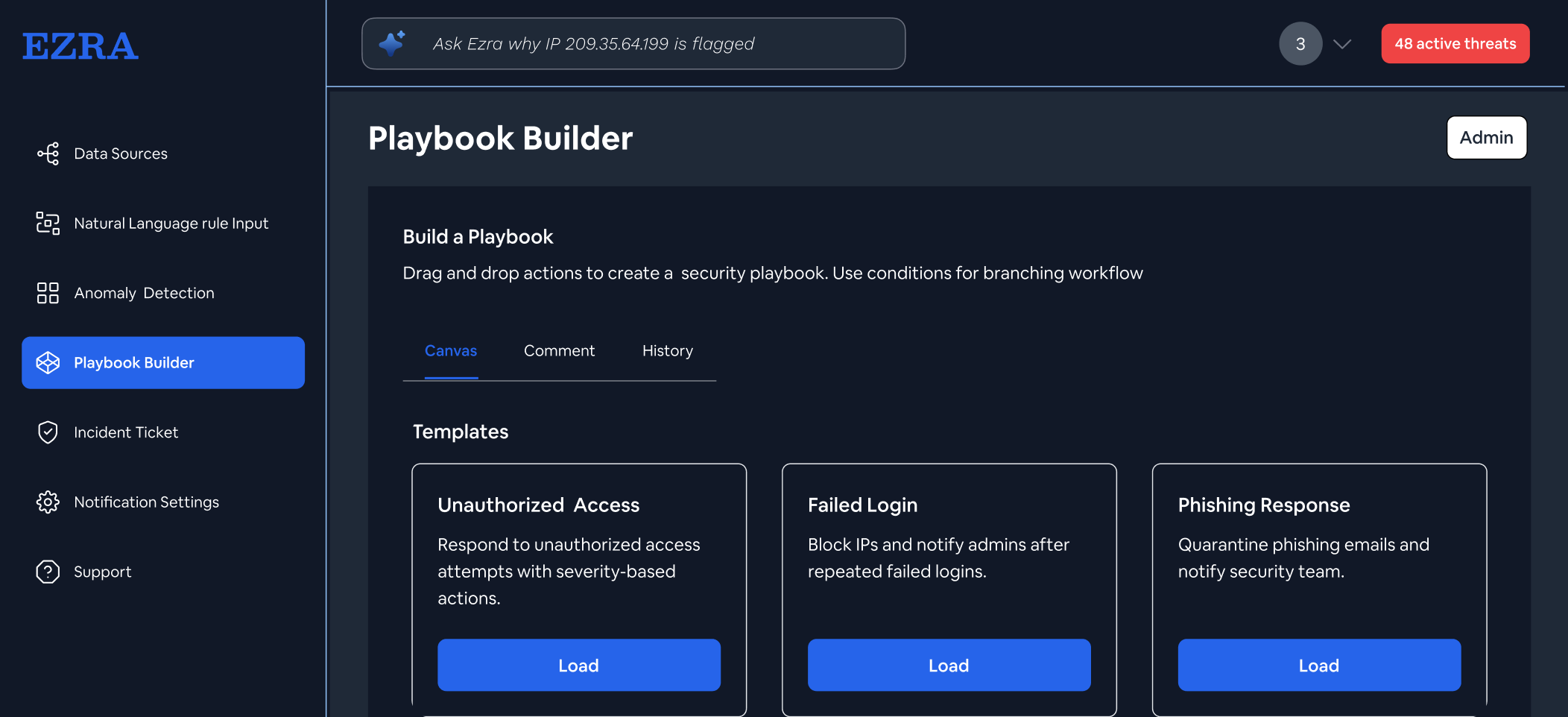
Create customizable playbooks to automatically respond to security incidents with predefined actions and responses
Collect, normalize, and analyze logs from all sources with powerful search capabilities and correlation rules
Get instant notifications about security incidents with detailed context to make informed decisions quickly
Gain a unified view of your security posture across on-premise, cloud, and hybrid environments from a single pane of glass
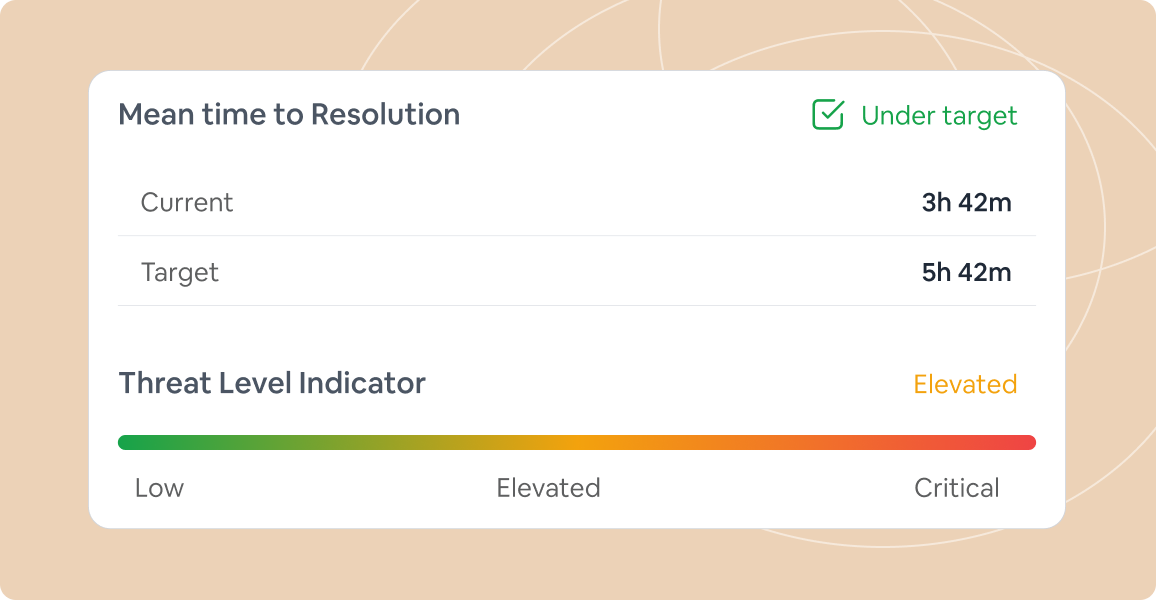
Track system performance and security health with customizable metrics and KPIs tailored to your organization
Connect with 200+ security tools and platforms to create a unified security operations center
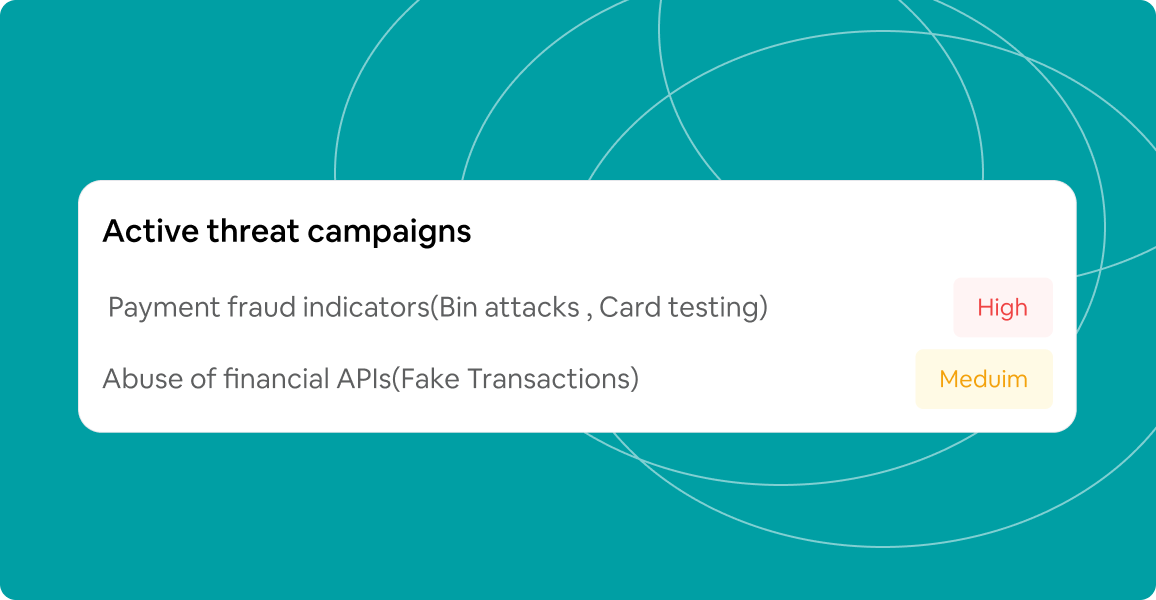
SOAR Automation can be applied across various security scenarios to enhance your team's capabilities
Automatically analyze suspicious emails, quarantine threats, and implement protective measures across your organization in minutes instead of hours
Identify infected systems, isolate them from your network, and deploy remediation actions to prevent lateral movement and data exfiltration
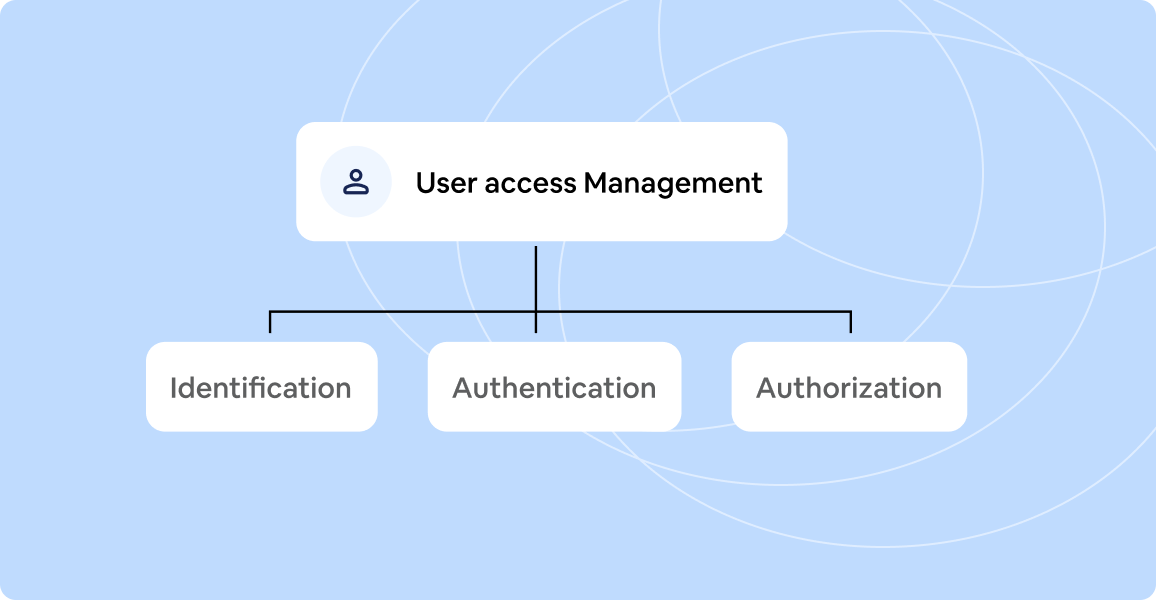
Monitor user behavior, detect unauthorized access attempts, and automatically implement access controls based on security policies.
Continuously scan your environment for vulnerabilities, prioritize based on risk, and automate patching workflows for critical systems
Our SOAR Automation platform streamlines your security operations through a simple yet powerful workflow
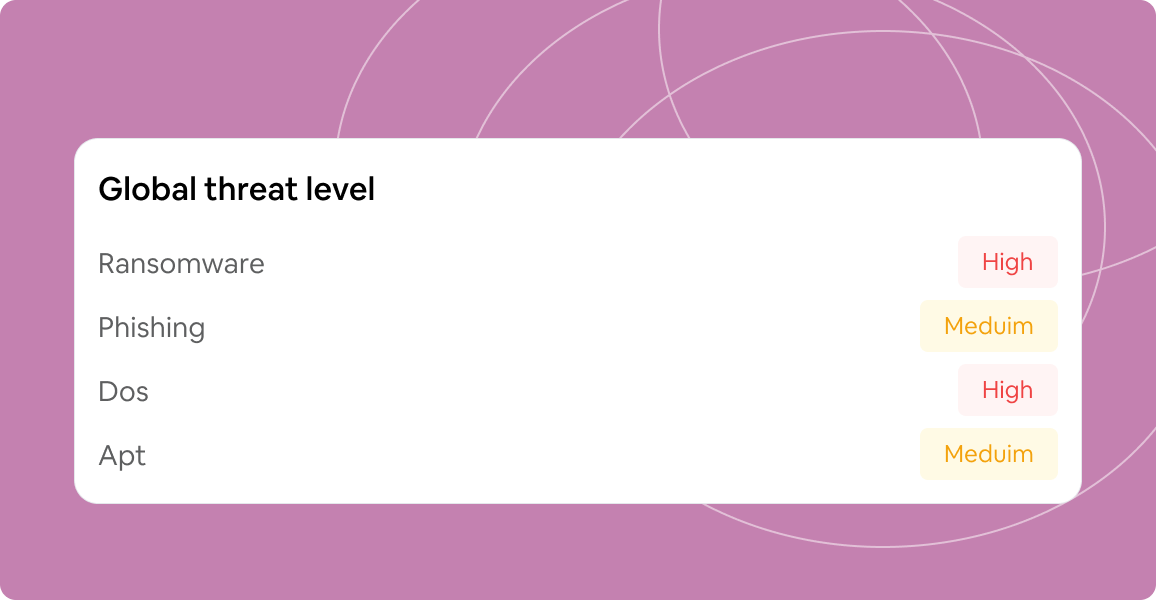
Our platform continuously monitors your environment for security incidents, anomalies, and potential threats using advanced detection algorithms and machine learning
Once detected, incidents are automatically analyzed to determine severity, impact, and appropriate response actions based on your predefined playbooks and rules
Automated response workflows kick in immediately, containing threats and implementing remediation steps while keeping your security team informed..
Our system continuously learns from each incident, improving detection accuracy and response effectiveness over time through AI-powered analytics
Our platform delivers measurable results for organizations of all sizes
99.9%
Uptime
Reliability
85%
Reduction in
Response Time
10B+
Events Processed
Daily
500+
Enterprise
Customers
Experience the power of our SIEM platform with a personalized demo tailored to your organization‘s unique security challenges
Scrubbe uses cookies and similar technologies to enhance your experience, analyze traffic, and enable personalized content. Choose your preferences below.
These cookies are necessary for the website to function properly. They cannot be disabled.
These cookies help us understand how visitors interact with the website, helping us improve our services.
These cookies enable personalized features and notifications to enhance your experience.
These cookies are used to track visitors across websites to display relevant advertisements.
