Impact Metrics
See the real-world impact of implementing Scrubbe Incident Management
60%
Faster Response Times
75%
Reduction in False Positives
45%
Lower Resolution Costs
Daily
99.9%
Incident Tracking Accuracy

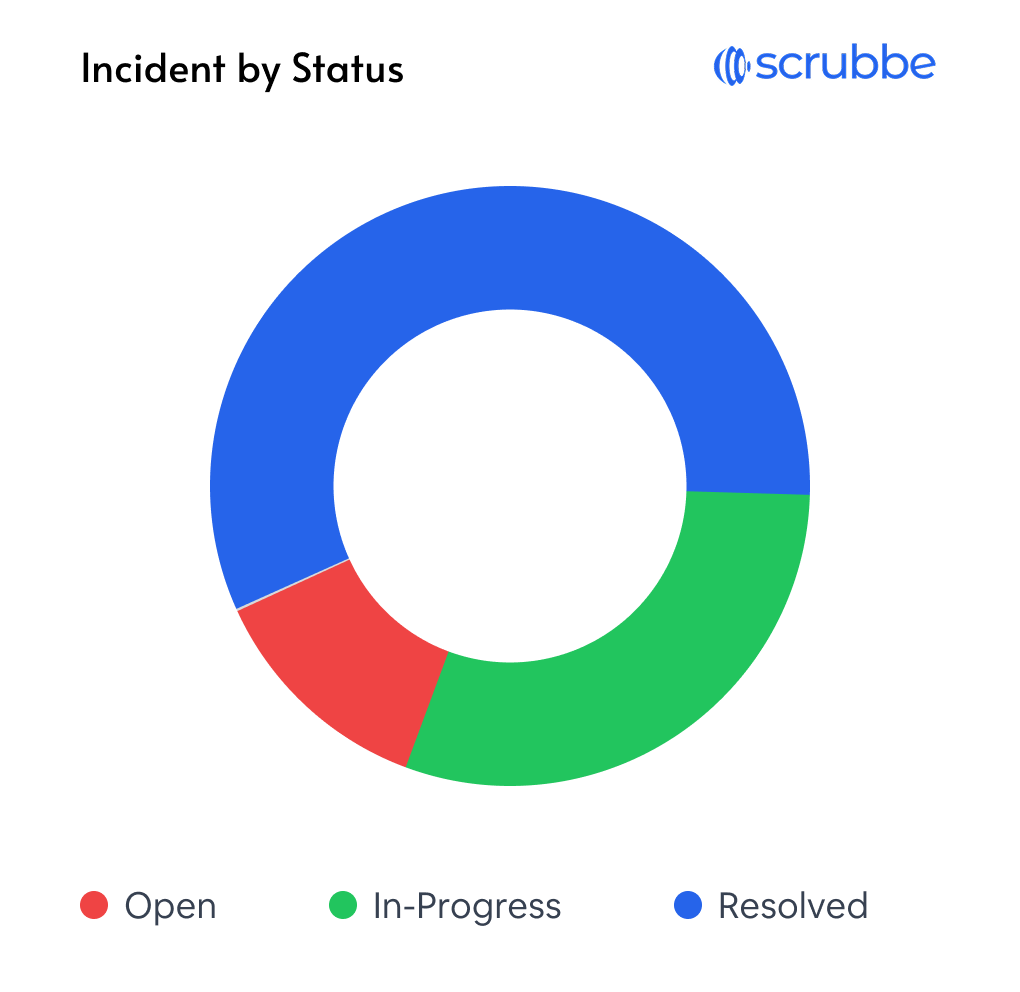
End-to-end visibility for security events from detection to resolution,
helping your team respond faster and more effectively.
Streamline your security incident response with these powerful capabilities
Identify security incidents as they happen with advanced threat detection and comprehensive alert monitoring
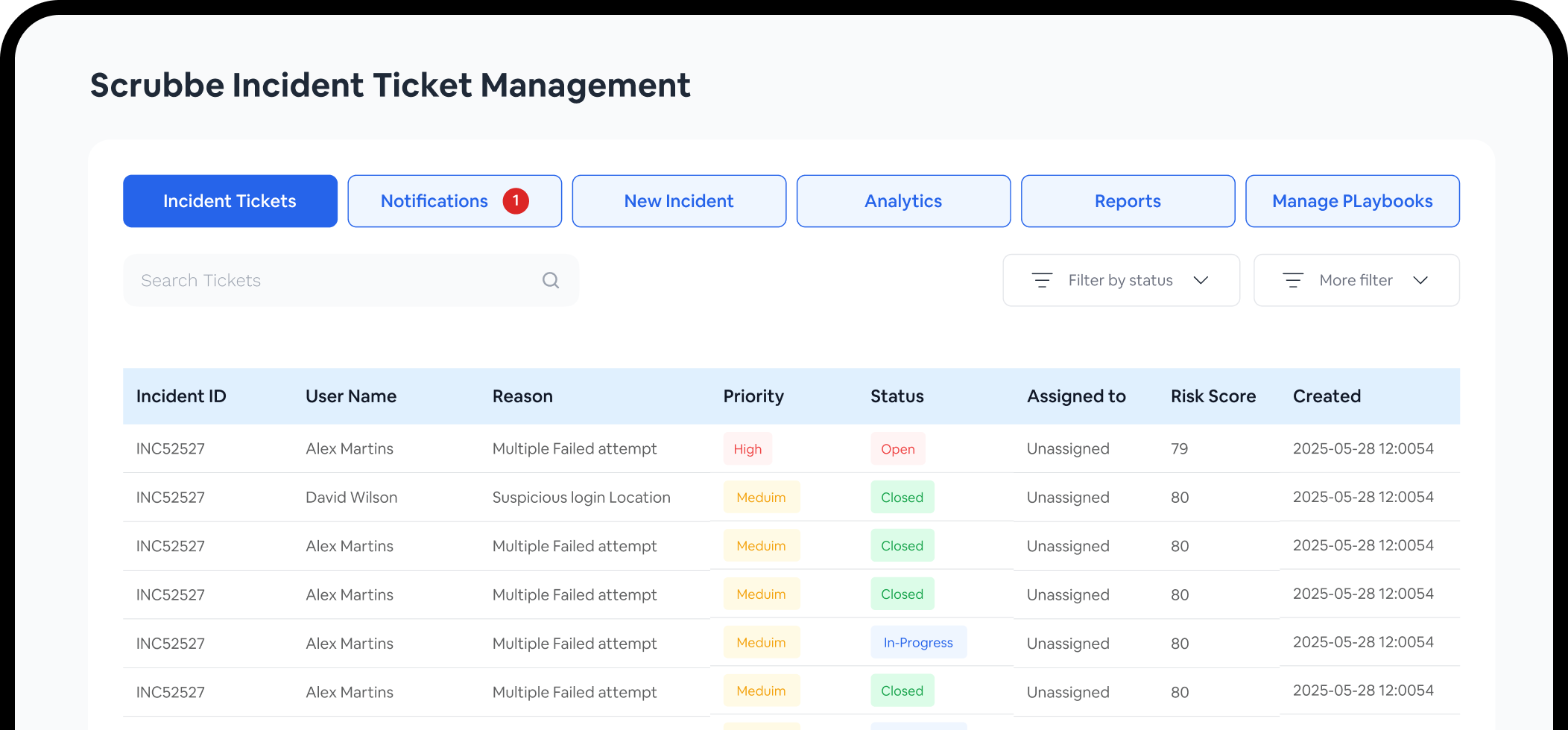
View all security events in one place with customizable dashboards for complete visibility across your organization
Streamline response with predefined playbooks and automation to ensure consistent incident handling
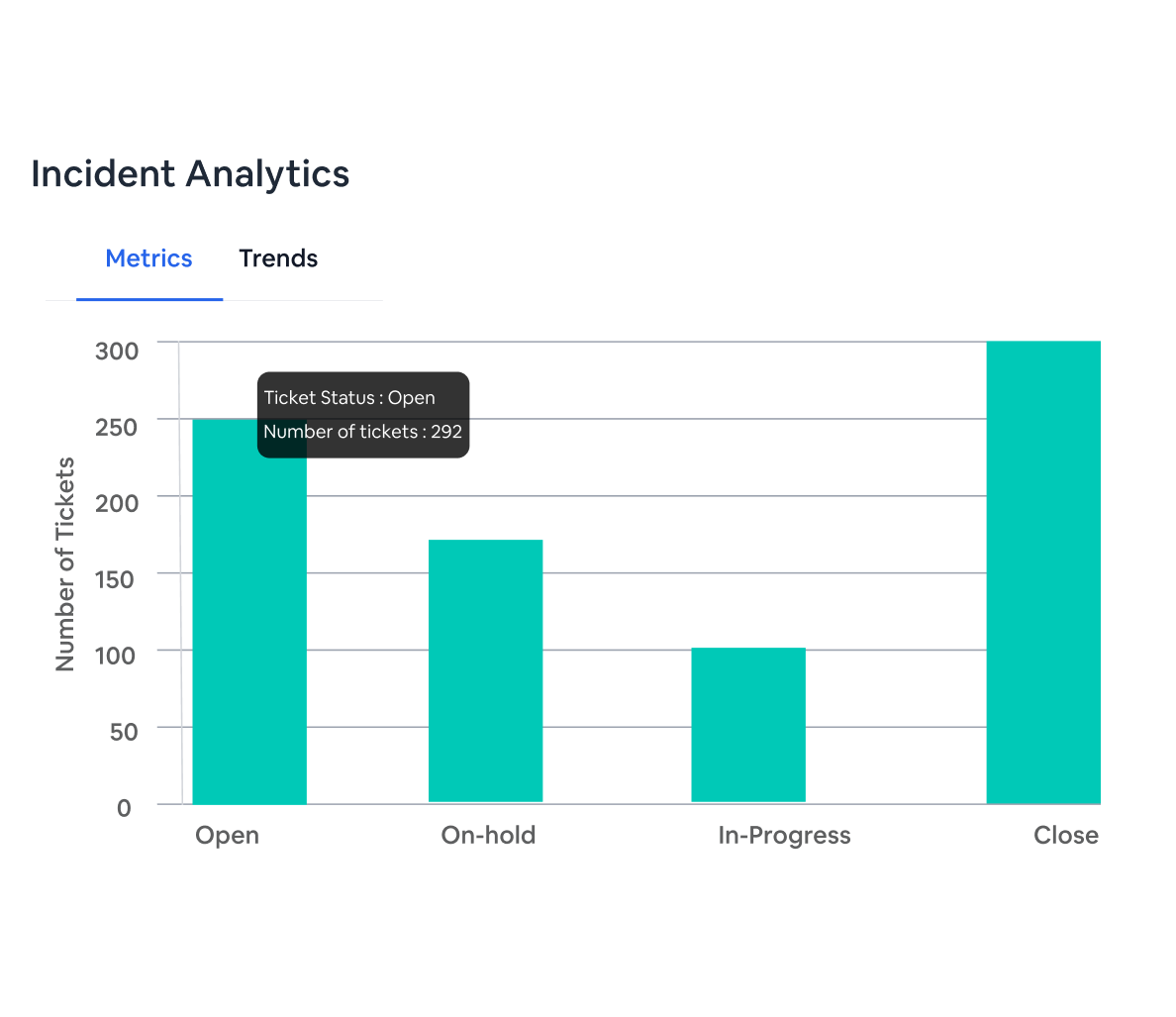
Generate comprehensive incident reports and analytics to improve future responses and meet compliance requirements
Enable seamless communication and coordination between security team members during incident response
Track the complete lifecycle of incidents with detailed event timelines for thorough investigation
Sample Incident Timeline
ID: INC-2023-05-13-001 | Unauthorized Access Attemp
08:45AM
Initial Detection
Multiple failed login attempts detected from IP 192.168.1.45 using brute force techniques
08:50AM
Automated Alert Generated
System generated high-priority alert and notified security team via SMS and email
09:00AM
Automated Response Triggered
IP address temporarily blocked by firewall as per security policy. Account locked for protection
09:10AM
Analyst Investigation
Security analyst John Doe started investigation, reviewed logs and initiated trace analysis.
09:15AM
Incident Report Generated
Detailed report generated with incident details, impact assessment, and recommended actions
09:30AM
Escalation
Incident escalated to Tier 2 response team due to potential data breach risk.
Generate comprehensive incident reports with all relevant details, actions taken, and outcomes to support compliance requirements and continuous improvement
Advanced algorithms detect security anomalies and trigger alerts based on customizable thresholds. Integration with your existing security tools ensures no threat goes unnoticed
Automatically categorize and prioritize incidents based on severity, impact, and organizational context to focus resources on critical issues first
Leverage built-in investigation tools and contextual data to quickly analyze incidents and identify root causes with comprehensive evidence collection
Execute predefined response playbooks to contain threats and remediate vulnerabilities, with options for manual intervention or fully automated responses
Generate comprehensive incident reports with all relevant details, actions taken, and outcomes to support compliance requirements and continuous improvement
Get a complete view of your security posture with our intuitive management interface
See the real-world impact of implementing Scrubbe Incident Management
60%
Faster Response Times
75%
Reduction in False Positives
45%
Lower Resolution Costs
Daily
99.9%
Incident Tracking Accuracy
Experience the power of our SIEM platform with a personalized demo tailored to your organization‘s unique security challenges
Scrubbe uses cookies and similar technologies to enhance your experience, analyze traffic, and enable personalized content. Choose your preferences below.
These cookies are necessary for the website to function properly. They cannot be disabled.
These cookies help us understand how visitors interact with the website, helping us improve our services.
These cookies enable personalized features and notifications to enhance your experience.
These cookies are used to track visitors across websites to display relevant advertisements.
